Malicious use of Eero
Eero and other extenders are being maliciously used in residential settings by bad actors to harass and turn over properties. The problem isn't exfiltration so much as using Eero with other access points to dump rogue sound on the devices of a neighboring house. Eero and other extenders are deployed in a manner that puts them over household infrastructure like AT&T NIDs, unused coaxial on the sides of houses and even electric meters and routers. I keep WiFi off and suspect that mesh networking allows another router to funnel data into my environment. I had professional heat maps done that show Eero 2.4GHz and 5GHz nodes around and over my house and giving access to rogue sound transmitted using cell phones from, for example, a parking strip of a neighborhood watch captain. The integration between Sonos and Eero seems to be used to great advantage -- I have ample Airtool captures showing sound between deployed to the Eeros that overlay my home and services and rebroadcast. I now suspect a powerline connection made be used to ensure that all my household wiring is enlisted in the transport of rogue sound. At my Seattle home, the infrasound dropped significantly when I had an old Comcast service box and coaxial removed. This kind of harassment is easily remoted via hot spots and conveniently parked cars and when I found the same harassment occurred when I began staying in my childhood home in the Bay Area, removing coaxial there was also useful and I found that the NID on that house was also being used when I had it removed, for sound in a higher range, it seems. I've seen other kinds of extenders such as TP-Link extenders which appear to be used to put WiFi signal on electrical lines and push signal inside, but Eero seems to play a key role in this type of harassment, perhaps because of the mesh network capabilities. I suspect that the Eero and other extenders may be able to connect to the access points and unadvertised SSIDs that Comcast and AT&T also provide or, with proximity to a target home, Eero deployment as an access point from which to transport rogue sound into someone's environment by physical networking and close-range transmission is sufficient.
I work in tech, have worked at a security company, and I am well aware of companies' interests in customer security. But what seems to be missing is our ability to assess the risk of the devices that are created and sold to be maliciously used against people who are not customers. In the case of cyber- or digital harassment, much of it is ignored because police don't know how to approach it and the belief is that those who do it are strangers whose anonymity is protected by network proxies, encryption and the like. This seems to have created an incredible opportunity for scams in the neighborhood, especially with IoT. In my case, this behavior represents the confidence of criminals and scammers that no one can "see" what they're doing. This is not true. Heat mapping can show the malicious deployment of extenders and how they are being used in crime. This kind of crime illustrates the lack of security of our homes, our residential infrastructure, and ultimately the grid. If your neighbors can use WiFi extenders and mesh networking to affect your devices, your network, and even your electrical system, so too can any terrorist.
I have a large amount of data and believe that what is happening to me can be mitigated by the creation of artificial intelligence. I have remained in an intolerable situation long enough to collect this data and to figure out how much of it works. I would like companies like Eero to help to ensure that their products are not used to effectively commit IoT crimes or acts of domestic terrorism. When digital harassment is taken up by hate groups, malevolent neighborhood watch groups or is made part of a business plan by real estate speculators, it's time for companies to assess security in terms of the impact of the products they make on people who are not their customers -- the greater community.
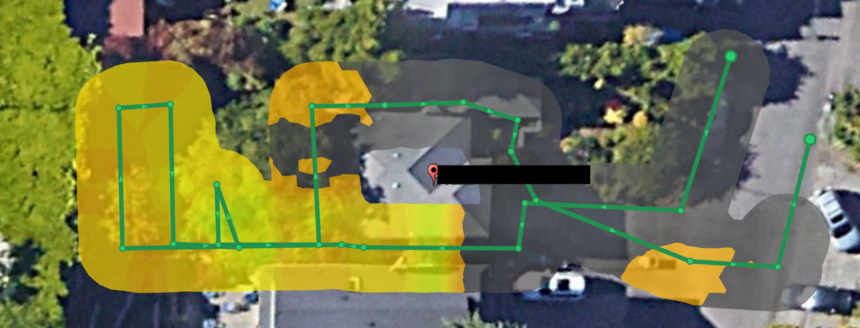
These screenshots show my home in Seattle and how my neighbors, who appear to be house flippers working in concern with the neighborhood watch, deployed your product. I considered adding but refrained from adding a Netspot survey that shows how at least four nodes were operating as the PowPow SSID and the Eye P.A. analysis showing the Sonos devices residing on the Eero nodes that are also identified by MAC vendor IDs. Note the open access points across the street. I think this is what some people who do not see the deployment of extenders consider to be "dashcam harassment." Unfortunately, it's worse -- it's infrastructure harassment or a means of putting rogue sound -- cyber-harassment -- on every device in a person's home using any copper wire on which transport is supported by a protocol.

8 replies
-
Something is definitely interfering with your communication, thinking, hearing, and reading comprehension abilities. Sorry you're having so much trouble. But I see no evidence it has to do with eero or Wi-Fi at all. There's no mention of either in the screenshots. Maybe consider the possibility that what you have isn't an electrical problem.🤗
-
You don't appear to be affiliated with Amazon and I suspect you either don't know much about heat maps and other WiFi surveys or are just trying to dismiss a type of malicious use that you might not understand or don't want to see exposed. You're probably not worth engaging with, but since you have tried to discredit not simply my report but my perceptions, I will respond.
Any network professional or anyone with a certain level of experience in configuring WiFi networks is likely to know about heat mapping and to how WiFi networks appear in heat maps. I posted professional heat maps and not my own NetSpot surveys. These professional maps are contained in files whose names reflect the Eero 2.4GHz and 5G extensions they represent. The files themselves are for Amazon/Eero to see. I posted them here because I want Amazon/Eero security to begin to look at the issue. When extensions are used to deploy rogue access points it's a risk for data exfiltration and injection. When extensions are deliberately used from outside your network to create interference and a powerline connection, there are greater risks to human health and safety.
It's unfortunate that communication on the web has been degraded to the point where one is forced to post legitimate product concerns that ultimately affect domestic security and the grid in forums like this one. I'll have to use PGP to communicate with Amazon/Eero security, apparently, or will have to send Amazon/Eero security a letter in snail mail that includes information that is not suitable for a forum, including a link to a Dropbox location that includes a lot of data that might be useful to develop AI to stop exploits using extenders (including the creation of a powerline or HomePNA connection) as well as heat maps that identify the repeaters as Eero products by MAC address.
You might consider some classes in networking and the 802.11 wireless protocol.
-
I thought this was a forum for discussion about technology, but it appears to be a forum of trolls who appear to set out to express hostility based on the aliases they adopt. There's nothing logical about flaming those with whom you share this space based on a lack of information and a lack of knowledge. This is the kind of thinking that has resulted the vast numbers of Covid-19 deaths and in uninformed mobs at the Capitol. Perhaps you got thrown off Twitter for your Qanon posts. What I describe is a network exploit based on principles of carrier current communications and boosting through the application of WiFi repeaters and the Eero in particular. It's a networking hack. You might not have been exposed to such a thing before but that's why we're here -- to learn from others. And if you've been doing networks for fortune 100 clients, you should understand the vulnerabilities that rogue access points pose in the enterprise.
This response is also for others on the forum who actually are here to discuss the issues people have with Eero. I would think that anyone in Texas right now has more serious issues on their hands with the recent weather and the infrastructure issues that have emerged. Good luck.
-
You posted this EXACT SAME THING on Reddit and got thoroughly crushed there over it. Out of professional courtesy, I sent a copy of your post there and this one to Netgear, Cisco, Asus, Linksys, Symantec, McAfee, Trend Micro, US CERT (Computer Emergency Response Team), and US DHS, and every one of them called your conclusion various polite forms of “bs”.
Moderators, please remove this thread.
-
I come late to this topic but I couldn’t leave without voicing my opinion. Sabatier is SPOT ON in her analysis of what is happening in our country. These bad players in my reality are meth labs run by the cartel. They have set up and teach these drug makers and hosts how to ice a community by driving out ppl from their homes and property. They poison livestock and the land. Destroy any erect buildings that could house security cameras to watch them. Use infrasound - ultrasound Thru the use of WiFi extenders to continue the harassment. Central California is the nations top meth producer and why? Because the ppl in charge have NO CLUE of the technology involved and how to deal with it. MUCH like ppl who can’t seem to wrap their small minded view of the real world and what’s happening around them until it comes to their front door. AND it will. I was told “Who you gonna tell? Who is going to believe you”
Content aside
- 3 yrs agoLast active
- 8Replies
- 3702Views
-
6
Following

